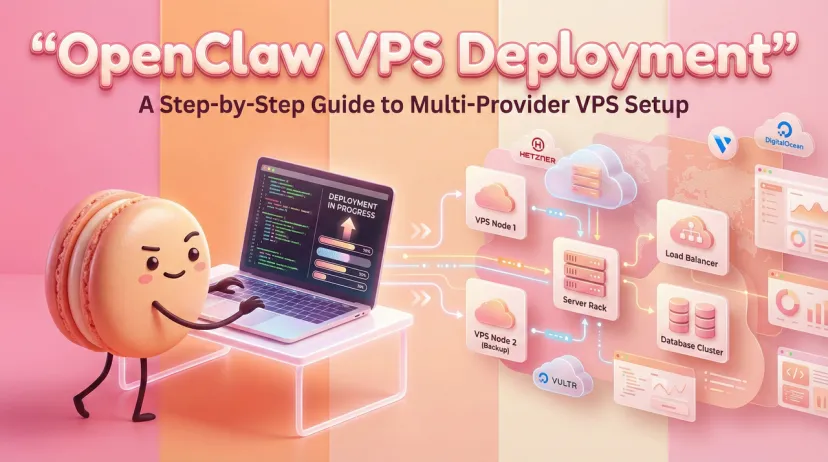
How to Deploy OpenClaw on a VPS: Hetzner, DigitalOcean, and Vultr Setup Guide (2026)
Hey fellow AI tinkerers — if you've been running OpenClaw on your local machine and wondering why it keeps going offline the moment you close your laptop, this one's for you.
I've been self-hosting AI agents for a while now, and the local machine trap is real. It sounds fine until you're on your phone at 10pm, your Telegram bot is dead, and you realize your Mac went to sleep three hours ago. I made that mistake twice before I finally moved everything to a VPS. That's what this guide is for.
I'm Hanks — I test automation tools inside real workflows, not demos. This is the setup I actually use, verified against the official OpenClaw VPS documentation as of February 2026.
The core question I kept asking myself when I first set this up: Can OpenClaw run reliably enough on a cheap VPS that I'd actually trust it with daily tasks? Let's find out.
Why Self-Host OpenClaw on a VPS?

Always-On vs. Local Machine Limitations
Here's the thing nobody talks about: OpenClaw is built around async, agent-driven tasks — browser automation, scheduled jobs, Telegram integrations. All of that breaks the second your local machine powers down.
Running it locally is fine for testing. For anything you'd actually rely on — scheduled reminders, inbox automation, channel integrations — you need a machine that doesn't sleep. A VPS is that machine. It runs 24/7, has a static IP, and gives you root access to configure everything properly. As the DigitalOcean OpenClaw tutorial puts it, a cloud server also gives you meaningful security benefits: container isolation, non-root execution, and hardened firewall rules that are harder to enforce on a personal laptop.
Recommended VPS Providers and Pricing (2026)
Based on current pricing and real deployment patterns, here's how the main options stack up:
Hetzner's CPX31 is my personal pick for anything going into daily use. Dedicated AMD EPYC vCPUs, NVMe storage, and EU data residency if that matters to you. DigitalOcean is the right call if you want to skip most of this guide — their 1-Click OpenClaw deployment handles a lot of the setup automatically.
Choosing and Provisioning Your VPS
Recommended Specs (RAM, CPU, Disk)
Per the OpenClaw server requirements documentation (updated February 2026), these are the real minimums:
- Text-only agent, no browser automation: 2 vCPU, 4 GB RAM, 40 GB disk — workable, but tight
- Standard use with browser skills: 4 vCPU, 8 GB RAM, 80 GB disk — solid
- Heavy automation, multiple channels: 4+ vCPU, 16 GB RAM — comfortable
The "minimum" spec (2 vCPU / 4 GB) will start OpenClaw. It won't handle browser automation sessions without getting sluggish. If you're enabling Playwright-based skills, budget for 8 GB RAM.
Choosing Ubuntu 22.04 LTS as Your Base
Ubuntu 22.04 LTS is the distribution the official docs test against, and it's what I'd recommend. It's stable, well-supported, and Docker's official install script handles it cleanly. Ubuntu 24.04 also works, but 22.04 has more community troubleshooting coverage for edge cases.
Initial Server Setup: User, SSH Keys, Firewall (ufw)
Once your VPS is provisioned and you have root SSH access:
# Create a non-root user
adduser deploy
usermod -aG sudo deploy
# Copy your SSH key to the new user
rsync --archive --chown=deploy:deploy ~/.ssh /home/deploy
# Switch to the new user
su - deploy
# Enable firewall — allow SSH, HTTP, HTTPS
sudo ufw allow OpenSSH
sudo ufw allow 80/tcp
sudo ufw allow 443/tcp
sudo ufw enable
# Verify status
sudo ufw status
Disable password authentication in /etc/ssh/sshd_config by setting PasswordAuthentication no, then restart SSH: sudo systemctl restart sshd.
Installing Docker on Your VPS

Official Docker Install for Ubuntu
Don't use the version from Ubuntu's default repos — it's often outdated. Use Docker's official install script instead:
# Install prerequisites
sudo apt update
sudo apt install -y ca-certificates curl gnupg
# Add Docker's GPG key
sudo install -m 0755 -d /etc/apt/keyrings
curl -fsSL https://download.docker.com/linux/ubuntu/gpg | \
sudo gpg --dearmor -o /etc/apt/keyrings/docker.gpg
sudo chmod a+r /etc/apt/keyrings/docker.gpg
# Add the Docker repository
echo \
"deb [arch=$(dpkg --print-architecture) signed-by=/etc/apt/keyrings/docker.gpg] \
https://download.docker.com/linux/ubuntu \
$(. /etc/os-release && echo "$VERSION_CODENAME") stable" | \
sudo tee /etc/apt/sources.list.d/docker.list > /dev/null
# Install Docker Engine + Compose plugin
sudo apt update
sudo apt install -y docker-ce docker-ce-cli containerd.io docker-compose-plugin
# Verify
docker --version
docker compose version
You should see Docker 26.x+ and Compose v2.x+. If you see "command not found" on docker compose, you've got the old standalone binary — the plugin version is what OpenClaw expects.
Adding Your User to the Docker Group
sudo usermod -aG docker $USER
newgrp docker
Verify with docker run hello-world — no sudo needed.
Deploying OpenClaw with Docker Compose

Cloning the Repo and Configuring .env
Per the official OpenClaw Docker documentation, the setup script handles most of the heavy lifting:
# Install git if needed
sudo apt install git -y
# Clone the repository
git clone https://github.com/openclaw/openclaw.git
cd openclaw
OpenClaw's docker-setup.sh script builds the image locally on your server, runs an interactive onboarding wizard, and writes your config to ~/.openclaw/. This means the first build takes a few minutes — subsequent rebuilds are faster thanks to Docker layer caching.
Key environment variables you'll configure during onboarding:
OPENCLAW_GATEWAY_TOKEN— auto-generated, but save it. You need it to authenticate the dashboard.- Your AI provider API key (Anthropic, OpenAI, or others)
- Gateway mode: choose Local so it runs on your VPS, not on external infrastructure
Running docker compose up -d
# Run the setup script (interactive — takes 3–5 minutes on first run)
./docker-setup.sh
# After onboarding completes, start in detached mode
docker compose up -d
The setup script launches two containers: openclaw-gateway (the main process) and openclaw-cli (for running management commands). Both need to be running for things to work correctly.
Verifying All Containers Are Healthy
# Check container status
docker compose ps
# View live logs
docker compose logs -f openclaw-gateway
# Health check via CLI
docker compose exec openclaw-gateway \
node dist/index.js health --token "$OPENCLAW_GATEWAY_TOKEN"
The dashboard is accessible at http://127.0.0.1:18789/ by default — local only, which is correct. We'll expose it properly through Nginx in the next section. If you need the dashboard URL with token, run:
docker compose run --rm openclaw-cli dashboard --no-open
Setting Up a Reverse Proxy with Nginx + HTTPS
Installing Nginx and Certbot
sudo apt install -y nginx certbot python3-certbot-nginx
sudo systemctl enable nginx
sudo systemctl start nginx
Make sure port 80 and 443 are open in your firewall (we did this in the provisioning step). Certbot needs port 80 to complete domain validation.
Config File for OpenClaw Dashboard
Create /etc/nginx/sites-available/openclaw:
server {
listen 80;
server_name your-domain.com;
location / {
proxy_pass http://127.0.0.1:18789;
proxy_http_version 1.1;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
# WebSocket support — see next section
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection "upgrade";
proxy_read_timeout 86400;
}
}
Enable the config and get your SSL certificate:
sudo ln -s /etc/nginx/sites-available/openclaw /etc/nginx/sites-enabled/
sudo nginx -t
sudo systemctl reload nginx
# Get HTTPS certificate
sudo certbot --nginx -d your-domain.com
Certbot will automatically modify your Nginx config to redirect HTTP to HTTPS and add the SSL block.
WebSocket Support — Critical Setting
Don't skip the WebSocket headers. OpenClaw's dashboard uses WebSocket connections for real-time updates. Without Upgrade and Connection "upgrade" in the proxy config, the dashboard will load but won't update live — and you'll spend 20 minutes wondering what's broken. I learned this the annoying way.
The proxy_read_timeout 86400 line also matters: without it, long-running agent tasks will get cut off mid-execution by Nginx's default 60-second timeout.
Keeping Your VPS Secure
Fail2ban and Login Hardening
Install Fail2ban to block repeated failed SSH attempts:
sudo apt install -y fail2ban
# Create a local config (don't edit jail.conf directly)
sudo cp /etc/fail2ban/jail.conf /etc/fail2ban/jail.local
sudo systemctl enable fail2ban
sudo systemctl start fail2ban
The default SSH jail bans IPs after 5 failed attempts in 10 minutes. That's usually fine to leave as-is.
Beyond fail2ban, the OpenClaw VPS security guide has a clear recommendation: keep the Gateway on loopback and access it via SSH tunnel or Tailscale — don't bind it directly to a public IP. If you must expose it, always require your OPENCLAW_GATEWAY_TOKEN. Never run without authentication.
For the gateway token itself: treat it like a password. If it leaks, anyone who finds it can interact with your agent.
Keeping OpenClaw Updated
OpenClaw has been shipping updates frequently (the version jumped from 2026.1.24 to 2026.1.30 in days). Check the OpenClaw GitHub repository for releases. To update:
cd ~/openclaw
git pull origin main
docker compose down
docker compose build --no-cache
docker compose up -d
Run the built-in doctor command after upgrades to catch configuration drift:
docker compose exec openclaw-gateway node dist/index.js doctor
Set a calendar reminder to check for updates weekly. This project moves fast.
VPS is live? Connect your first messaging channel — see our WhatsApp Setup or Telegram Setup guides to start automating.
Frequently Asked Questions
Q: What's the minimum VPS I can actually run OpenClaw on?
The hard floor is 2 vCPU and 4 GB RAM. Below that, Docker becomes unstable during skill loading. At 4 GB, you can run a text-only agent reliably. Browser automation needs 8 GB. Don't cheap out on RAM — it's the first thing you'll regret.
Q: Do I need a domain name, or can I use my VPS IP directly?
You can use a bare IP — just skip the Certbot step and access the dashboard over HTTP on port 18789. For anything beyond local testing, I'd get a domain and set up HTTPS. It takes 10 minutes and means your browser stops yelling at you about insecure connections.
Q: Hetzner vs. DigitalOcean — which should I actually pick?
If you're in the EU and care about data residency or GDPR, Hetzner CPX31 is better value per euro and the network performance is solid. If you want the simplest possible setup with a 1-Click deploy, DigitalOcean's marketplace option gets you running in minutes with security hardening already configured. I run Hetzner personally, but I've pointed beginners to DigitalOcean's 1-Click without regret.
Q: My containers started but the dashboard won't load. What's wrong?
Three things to check in order: (1) Is port 18789 actually bound? Run docker compose ps and confirm the gateway container is "Up". (2) Did you include the ?token= parameter in the URL? Run docker compose run --rm openclaw-cli dashboard --no-open to get the full URL. (3) If you're going through Nginx, did you add the WebSocket headers? Missing Connection "upgrade" is the most common cause of a dashboard that loads but feels broken.
Q: Can I run OpenClaw on the same VPS as other services?
Yes, as long as you have enough RAM. Just make sure there's no port conflict on 18789 and your Nginx config routes cleanly. If you're running other Docker services, use a shared network and be explicit about container naming.
Last verified: February 2026 against OpenClaw v2026.1.30, Docker Engine 26.x, Ubuntu 22.04 LTS